Table of Contents
Azure Key Vault > Azure Automation Credential Manager
Azure Automation has its own Credential Manager.
This is the easiest to use, but has no history or version control.
So you can’t see when the value was last changed, or who made the change within the portal (this can be done via Log Analytics).
The Azure Key Vault can do this and much more. This makes the Key Vault also useful for Azure Automation.
You can implement a Key Vault in your Azure Automation environment via PowerShell scripts & Managed Identity.
Below I explain to you how this is possible and how you can use the PowerShell functions in your environment.
Do you have any questions, or do you see something that could be improved?
Then I’d love to hear about it in the comments.
Via a module or separate PowerShell functions?
I offer you the solution in two ways.
- In a PowerShell module
- Two separate PowerShell functions
Both have its advantages. Read the below carefully.
If you only run runbooks in the Azure sandbox (cloud), a PowerShell module is more convenient. Also because it makes it easier to get updates etc.
But if you use hybrid workers, the module must also be installed on the hybrid workers. Via the PowerShell functions you can dot source the scripts to your hybrid worker from the cloud.
This is not yet possible with the modules. In this way you only have one dependency and that is the PowerShell function in Azure.
Is it not possible to use the module when using hybrid workers?
Certainly yes, only then you also have to install the modules on the hybrid workers.
Follow these steps if you want to use the PowerShell module in conjunction with the Azure Key Vault
- Open the appropriate Azure Automation environment
- Go to modules
- Click on Add a module
- Select Browse from gallery
- Click Click here to browse from gallery
- Search for Optimized.AzAutomation
- Import the module
You will now see the module in the list of installed modules in the Azure Automation sandbox.

Now follow the steps in section Enable Managed Identity.
Follow these steps if you want to use the PowerShell functions on a hybrid worker without module dependencies
Go to my Github repository BasWijdenes and search for the following two files:
Get-KeyVaultCredentialNew-ManagedIdentityAccessToken
They are two separate PowerShell functions because they are both generic, making, for example the New-ManagedIdentityAccessToken more widely applicable.
Continue with the steps below.
Get-KeyVaultCredential function
- Create a new runbook in Azure Automation and name it
Get-KeyVaultCredential.
Keep the name as they are in Github so that the functions can call each other. - Copy the script content from Github into the runbook and publish it.
New-ManagedIdentityAccessToken function
We also need the New-ManagedIdentityAccessToken function.
This can also be found on Github.
Through this function we request an authorization token for the Azure Key Vault.
Place it in Azure Automation in the same way as the Get-KeyVaultCredential function.
You don’t need to dot source or implement it. This is done automatically by the function itself.
How can we use this in runbooks in the future?
In Azure Automation you can make handy use of dot sourcing.
Dot sourcing means that you ‘paste’ the script into the existing script.
You do that this way:
. .\Get-KeyVaultCredential.ps1So the relative path to the script & a dot.
And don’t forget the .ps1 filename extension.
This way the script is pasted into your runbook and you can call the appropriate functions. This works in the Azure sandbox & hybrid workers.
You can also dot source New-ManagedIdentityAccessToken, but this is also done by Get-KeyVaultCredential.
For more about dot sourcing I’d like to refer your to Microsoft Docs.
Enable Managed Identity
We need to enable Managed Identity in Azure Automation and give it permissions to the Azure Key Vault with at least read secrets permissions.
Microsoft Docs has a tutorial to enable the Managed Identity:
Using a system-assigned managed identity for an Azure Automation account | Microsoft Docs
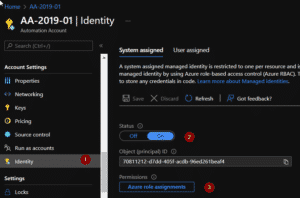
You can assign access to the Azure Automation Managed Identity in two ways.
Via Access Policies or RBAC.
Microsoft Docs has a tutorial for both.
The choice is yours.
- Assign an Azure Key Vault access policy (CLI) | Microsoft Docs
- Grant permission to applications to access an Azure key vault using Azure RBAC | Microsoft Docs
The Managed Identity name is the name of your Azure Automation environment.
The screenshot shows my Access Policies.

Now let’s start using the cmdlets!
Do you use the separate function? Don’t forget to dot source Get-KeyVaultCredential.
The UserName parameter is the secret name in the Azure Key Vault.
I mainly use the cmdlets for credentials, so the cmdlet automatically turns them into a user. You automatically receive a Credential Object that you can use as credentials without seeing the secret as plain text.
Below is an example.
Get-KeyVaultCredential -UserName 'TestUserName' -KeyVault 'KV-XXXX'
UserName Password
-------- --------
TestUserName System.Security.SecureStringA credential object is not always usable.
For this I made the -SecretOnly switch that ensures that you get the value back as plain text.
Get-KeyVaultCredential -UserName 'TestUserName' -KeyVault 'KV-HR-XXXX' -SecretOnly
TestUserValueAnd that’s it. From now on you can use the Azure Key Vault in collaboration with Azure Automation instead of the built-in credential manager.